Are you wondering which one to choose between SecDevOps vs DevSecOps in your Systems Development Life Cycle (SDLC)? Well, you are not alone.
We all crave total security. We want our web applications, systems, and organisations to be completely secure without suffering from any vulnerabilities. However, there is no such thing as total security, or is there?!
The landscape of cyber threats today is evolving quicker than ever before. In light of recent high-profile common forms of data breaches, it is clear that we must begin to prioritise cybersecurity in software development.
Both the options in the comparison of SecDevOps vs DevSecOps provide the necessary security-first attitude we need in today’s world. They both address the requirements for the quick modification of software and identify and repair security gaps as soon as they are discovered. They also continually deploy novel defensive solutions to catch bad actors off guard.
We require a structure to coordinate and oversee our security initiatives. Value Stream Management (VSM) assists SecDevOps and DevSecOps teams to be on the same page by establishing end-to-end visibility and controlling workflows for continual compliance.
“Read More: What Does a CISO Need to Know?”
What Is Software Development Life Cycle (SDLC)?
Before getting to the winner of SecDevOps vs DevSecOps, we should know more about SDLC. Software/Systems Development Life Cycle (SDLC), also known as Software Development Process (SDP) or Software Development Model/Method/Methodology (SDM), refers to the procedures and methodologies implemented by software companies.
Companies use different SDLC models to develop and deliver exceptional software that transcends what users want from them with the given resources and timeframe. You can think of it as a thorough framework that defines what should be done at each stage of development.
Note: Do not confuse SDLC with the ISO/IEC 12207 standard. This standard only defines specific processes, not stages, for the software’s lifecycle.
SDLC typically offers a detailed scheme and methodology for the development, maintenance, replacement, alteration, and enhancement of applications.
The following figure is the summary of all of the SDLC stages and models:
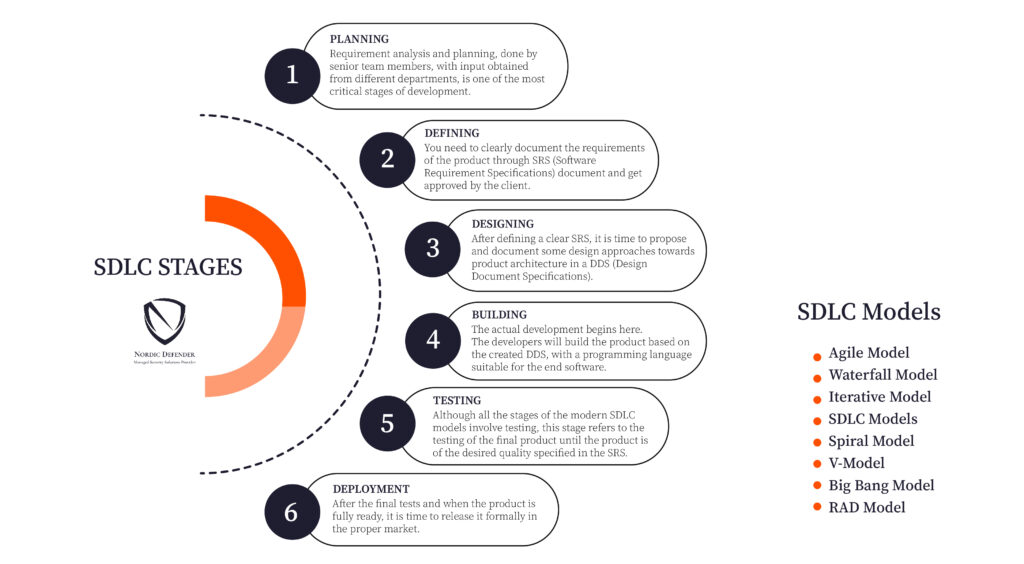
In order to understand the challenges of SecDevOps vs DevSecOps, first, we need to get into more detail about the SDLC stages.
- Planning
One of the most fundamental and critical stages in SDLC is the planning stage. Senior team members get inputs from the end customers and different departments in the company and combine them with the results of market surveys and information they get from industry leaders.
After they process all of this information, they use it to plan the project approach, product feasibility study, quality assurance requirements, and risk identification. In the planning process, they will finalise the plan that comes with minimum risks and has a higher chance of success after implementation.
- Defining
Whichever you want to choose between SecDevOps vs DevSecOps, after fully conducting the requirement analysis, it is time to define and document the requirements of the product. It is of great importance to get the documentation approved by both the end customer and the market analysts.
This is where an SRS (Software Requirement Specification) document comes to help. An SRS document involves all the requirements of the project that are to be designed and developed in the SDLC.
- Designing
Designing the architecture of the product is a vital stage towards having foolproof software. Product architects come up with many designs based on the SRS and the requirements defined in it. They document these designs in a DDS (Design Document Specification).
The DDS is then proposed to the stakeholders of the company. Afterwards, based on different parameters, the best product architecture will be chosen.
Learning all about SecDevOps vs DevSecOps can help you tremendously at this stage of the product.
All the architectural modules of the product and its data flow representation will be covered in the design. More importantly, the proposed DDS must contain the design of the internal modules, communication representation, and third-party modules.
Assess the robustness of your infrastructure with Nordic Defender’s Red Team Assessment and stay safe in the cyber realm.
- Developing
Depending on the product and the type of software needed, a programming language is chosen at this stage. Whichever you choose between SecDevOps vs DevSecOps does not influence the choice of programming language.
The product will be built without much hassle if the design and architecture are created professionally.
- Testing
All stages of the SDLC so far involved testing at some point. This stage solely refers to the final testing stage, when the product is nearly final. The bugs will be reported, traced, and hopefully fixed at this stage. The product will be tested again and again until it provides the desired quality.
- Deployment
After fully building and testing the product, it is high time you release it to the proper market. Depending on the business strategy, deployment may happen in stages. After getting feedback from the users, enhancements and bug fixes will be made continuously. This stage plays a huge role in the comparison between SecDevOps vs DevSecOps.
Different SDM Models
If you know all about everything and just want to get to the comparison between DevSecOps vs SecDevOps, just skip ahead.
However, if you want to know more, you should know that there are different SDLC models out there, also referred to as Software Development Process Models (SDPM). During the SDP, each process model can be used to approach successful software development.
There are many different models; however, the following list includes the most used methodologies:
- The Waterfall Model
- The Iterative Model
- The Spiral Model
- The V-Model
- The Big Bang Model
- The Agile Model
- The RAD (Rapid Application Development) Model
Before reading on, keep in mind that in different value streams, different things need to be secured:
| Applications | Infrastructure | Pipelines | |
| Planning | Budgets, schedules | Budgets, schedules | Budgets, schedules |
| Design | Architecture Components Features | Deployment environment – automation | Tools – Toolchains – Automation |
| Integration | Features – Releases – Artifacts | Features – Releases | Features – Releases |
| Pre-Production | Acceptance – Deploy Preparation | Acceptance | Acceptance |
| Production | Operations – Metrics – Anti-Fragility – Post-Mortems | Operations – Metrics – Anti-Fragility – Post-Mortems | Operations – Metrics – Anti-Fragility – Post-Mortems |
SDM Models Before SecDevOps
Now that we know what SDLC is and its different models, it is time to learn more about its models and the history behind them before we get deep into SecDevOps vs DevSecOps.
The Waterfall SDM
The Waterfall model started around the 90s. It was a rigid model that only accepted sequential project management. Everything should be linear for the Waterfall SDM to work, and you cannot start the next step until and unless what you have at hand is completed.
There are six stages in the Waterfall SDLC, and each should be paved carefully:
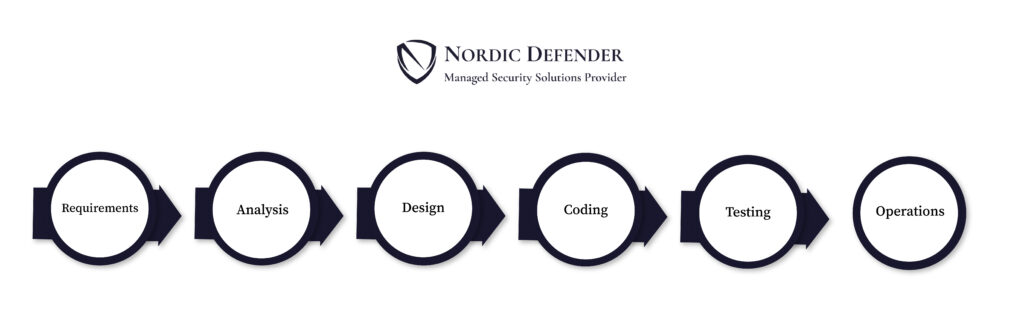
Let us give you an example to provide you with a better understanding.
Imagine a software developer by the name of Mike is offered a project from a finance company. What would Mike need to do if he wants to comply with the Waterfall SDLC? Which one should he go for in the SecDevOps vs DevSecOps competition?
Well, first, the project team must obtain the needed input and create the SRS. Afterwards, the team would continue planning and designing the structure of the application. After finalising the SRS, the development team can start developing the application.
What would happen if the finance company missed a requirement and wanted to add a new field in the middle of the process? This is where things go wrong, and you will shortly see that none of the options in the competition of SecDevOps vs DevSecOps would be usable.
In the Waterfall SDLC, no new features or missed prerequisites are not going to be developed till the implementation phase is over! There is no room for changes/additions in this methodology. Everything is rigid, unproductive, and ineffectively slow.
Mike would always miss deadlines and delivery milestones due to missing different specifications/requirements that were not outlined at the right time. Every simple project would take years to complete.
Generate thorough reports without false positives with Nordic Defender’s Intelligent Discovery and benefit from the alliance of machines and humans.
Now, do you think that choosing DevSecOps vs SecDevOps could be added as a part of this mess? Absolutely not! Without application security, most deadlines were missed due to all the mess in the Waterfall system. Adding more complexities, like security, would surely not be of any help!
Waterfall and Application Security
SecDevOps vs DevSecOps has made quite a controversy in today’s world; however, back then, security was not seriously considered at all. At that time, Personal Computers (PCs) and the Internet of Things (IoT) were considered innovations, and the world was focusing on the Bring Your Own Device (BYOD) concept.
After eventually realising the frustrating pitfalls of the Waterfall SDM, organisations decided to break free. This is where the Agile Manifesto was born with twelve principles in mind. The Agile Manifesto emphasised:
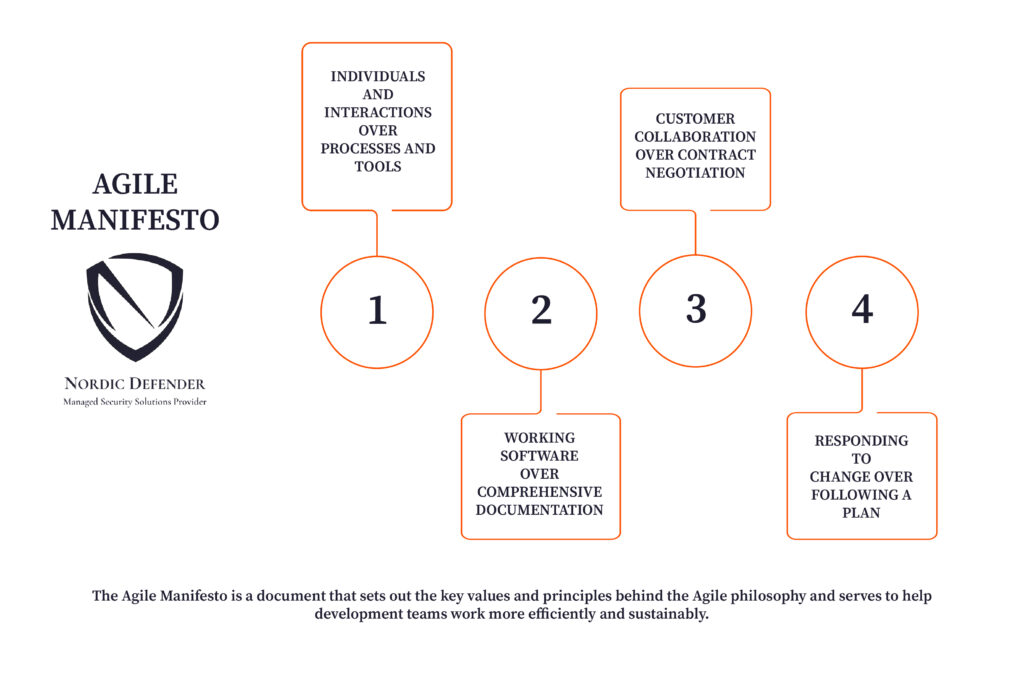
- Individuals and interactions over processes and tools
- Working software over comprehensive documentation
- Customer collaboration over contract negotiation
- Responding to change over following a plan
The Waterfall SDLC did not care about customer involvement; on the other hand, the Agile methodology mainly focuses on users and their interactions with the software.
This methodology eliminated bottlenecks and enabled developers to deliver their applications at a tremendously faster pace. The well-timed and recurrent interactions between developers and stakeholders empowered them to come up with better ideas and deliver better end results.
This was a critical stage in the path to the SecDevOps vs DevSecOps competition.
Agile SDM
No matter which you choose between DevSecOps vs SecDevOps, the choice you make comes from an Agile point of view. The Agile methodology is all about continuous, iterative development and testing between cross-functional departments.
It starts with defining the users, developing a vision statement, and pinpointing opportunities, and it ensures that everybody is thoroughly acknowledged of the product, the responsibilities, and the needed collaboration.
Application Security in Agile
Agile implemented a user-rights-based mechanism. In this mechanism, the product owner is the head, repositories keep track of changes and updates to the so-called user story, and any necessary updates to requirements are potentials given to all of the system’s users.
Before reaching the time when SecDevOps vs DevSecOps became a concern, security was always an afterthought. It had no place throughout the process of software development, even in the Agile SDLC. Although Agile was a massive improvement over the Waterfall SDLC, it still lacked many aspects and could not be called the perfect methodology.
What is DevOps?
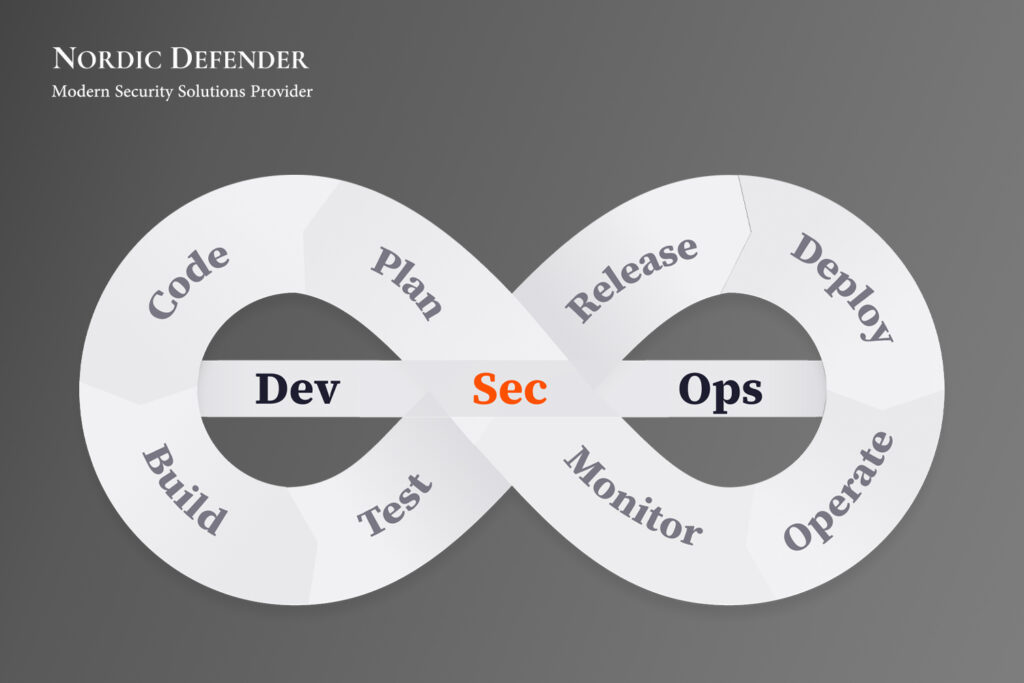
The last thing there is to know before finally getting into DevSecOps vs SecDevOps is to know the repetitive part in the two—DevOps. So, what is DevOps exactly?
As you already know, after the failures that the Waterfall model faced, the Agile methodology gained popularity. However, we also saw that even Agile was not the optimal solution. This is where DevOps came to the rescue.
DevOps—Development and Operations—was the new development culture everybody needed. DevOps is the fusion of people, procedures, and end products. What makes DevOps special is the Continuous Integration and Continuous Delivery/Deployment (CI/CD), which enables the end users to enjoy a seamless experience.
The race to defend against attackers must accelerate to match the increasing pace of attacks. DevOps can be helpful in achieving this.
Whichever you are going to pick and implement between SecDevOps vs DevSecOps, keep in mind that applications get more complex each day. This results in increased attack surfaces and vulnerabilities, such as:
- Distributed apps
- Distributed infrastructures
- Distributed pipelines
- Supply chains.
At the same time, attackers’ sophistication is increasing as well. These factors contribute to this fact:
- More attackers
- Attackers gaining experience
- Maturing attack capabilities
- Increased attacker collaboration
- Attacker success stories.
Most importantly, as a result of all of these, the impacts of security breaches are increasing. This is why you should choose wisely when you want to decide on SecDevOps vs DevSecOps. Take the following examples into account:
- A state-sponsored threat group from China exploited zero-day vulnerabilities in Microsoft Exchange Server.
- Acer Computer was attacked with ransomware demanding $50 Million from them.
- Ransomware attack shut down biggest U.S. gasoline pipeline.
- A backdoor was used to get access to and leverage SolarWinds’s supply chain to compromise multiple global victims.
- Hackers used Pulse Secure vulnerabilities to breach multiple agencies in U.S. and Europe.
- Ransomware attacks struck between 800 and 1,500 businesses.
- The WannaCry ransomware attack was a worldwide cyberattack in May 2017 by the WannaCry ransomware cryptoworm, which targeted computers running the Microsoft Windows operating system by encrypting data and demanding ransom payments in the Bitcoin cryptocurrency.
Security failures mostly affect the entire enterprise (clients’ data leakage, networks shutting down, etc.) rather than services, zones, or features which are typically caused by functional/performance failures. This is why security needs attention in DevOps pipelines.
For the most part, in the history of DevOps, security was not seen as a concern. The main focus was getting out of development chaos and CI/CD concepts.
Start using Nordic Defender’s Threat Detection as Code and ensure optimal safety.
You can start to see what the role of DevOps is in SecDevOps vs DevSecOps.
Waterfall and Agile models were mostly linear and sequential; however, DevOps relates to Agile practices that enable process automation to bring the software development team closer to the other departments. This is what provided the new ecosystem of development and operations teams with proactivity in their SDLC.
“Read More: Can Cybersecurity Be Outsourced?”
Automation is a tool that runs and does a bunch of stuff. Orchestration is the combination of manual and automated tasks using disparate tools. The purpose of bringing value stream management as it relates to security is to bring all data to a single place, orchestrate across the various activities that need to happen (planning – delivery), and give you analytics to show you how you are doing.
Even though the attitude behind DevOps was not far away from Agile, you should note that DevOps was a paradigm shift. The CI/CD delivery process eliminated latency among different departments and stakeholders all in all and empowered them to have better communications and synchronicity. This is also what makes both options in SecDevOps vs DevSecOps so special.
DevOps continuous security makes sure you do not need to redo your architecture in the middle of the process because of a security threat. You will not need to add stuff that brings massive risks and destabilise your product. You think about security first and in the whole process.
Containers, microservices, and many other innovations have made automation way more achievable than before. This not only made the process easier but also ensured that security both was a part of the process and was integrated at different stages in the SDLC.
What is DevSecOps?
After all this talk, it is time to get to the first part of the comparison between DevSecOps vs SecDevOps. We have used its name many times during this article; however, we have not explicitly talked about it yet.
DevSecOps is basically DevOps plus the Security component and is one way that security can be integrated into the DevOps process. Both DevSecOps and DevOps share the same mission; however, DevSecOps puts more emphasis on security.
As you remember, security had always been an afterthought before DevOps. DevOps was basically the same as DevOpsSec at that time, and the developer was not required to minimise the vulnerabilities his application came with.
When we talk about SecDevOps vs DevSecOps, we must consider one thing. With the shift that came with DevSecOps (security literally shifted one towards left), everybody in the process was required to put security into practice in their role. Developers were supposed to develop their codes carefully and with regard to guidelines such as CERT, OWASP, CWE, PCI-DDS, UL-2900, etc.
DevSecOps practices integrate security practices within the DevOps process:
- Cultural aspects of Security as Code (SaC)
- Engineering security into design and deployment processes
- Remove security as a bottleneck with continuous delivery pipelines
- Bridge gaps with security practices while ensuring fast, safe deliveries
- Replace isolated team practices with increased communication and shared responsibility for security tasks during all phases of the delivery process.
There is a reason why DevSecOps came into play at first. DevOps was great, but there was still room to grow. DevSecOps was created out of a need.
Sometimes, there was tremendous pressure on all teams to deliver the product. This meant that the magical collaboration of developers and the QA department to achieve security would diminish. What happened is that security turned out to be an afterthought again.
In today’s world, the companies that choose DevSecOps in the SecDevOps vs DevSecOps comparison bring in a separate team of expert security professionals. Not only everybody in the organisation must learn and practice security in what they do, but also security-focused professionals who are tasked with finding vulnerabilities.
A set of standards and guidelines enables security practitioners to eliminate insecure coding practices and complicated APIs. Making everything more efficient and effective, CI/CD pipelines can help automate application security testing and application updates.
If you still do not know which one to choose in SecDevOps vs DevSecOps, or if you think of software security as a nice-to-have feature and not as a critical demand, keep reading.
DevSecOps Best Practices
If you think DevSecOps is the choice you are going to go with between SecDevOps vs DevSecOps, you need to know its best practices. This ensures that you get maximum efficiency out of this methodology.
Enhance Communications Between Developers and Security Experts
As you saw earlier, the DevOps principles aimed to eliminate the blockade that separated engineering and operation teams. The DevSecOps philosophy goes one step further and does its best to break down the barrier between engineering and security teams.
Encourage Security Testing at Each Stage
DevSecOps brings a paradigm shift just like DevOps itself. There are two approaches towards this immense change in culture, and neither of them is easy to integrate; however, each organisation must determine which approach suits them best to resolve security issues before the application is out.
- The executive staff and managers hand out the changes to all other employees.
- Cross-team security cooperation starts from the bottom and expands to other teams.
Automate Jira Ticket Creation
No matter which one you choose between SecDevOps vs DevSecOps, you should note that every team engineering and IT security team yearns for efficiency. This is why one of the best practices in DevSecOps is automatically creating Jira tickets for the identified vulnerabilities. After the remediation of the vulnerability and verification of the fix, the Jira ticket should automatically get closed.
What is SecDevOps?
We have so far discussed DevSecOps in our comparison between DevSecOps and SecDevOps. So, let us see what SecDevOps has to offer us.
As it is clear, SecDevOps pushes security one more step to the left. This is not just wordplay. SecDevOps, quite unlike the pre-DevOps era, brings security practices—which were considered an afterthought back then— to the beginning. The security of the applications is now a priority, and all the stages of SDLC are based on secure coding practices.
Furthermore, considering constant communication the key to success, SecDevOps ensures optimum collaboration among all departments, especially the cooperation of the operations team with others.
SecDevOps practices put security first. Security is not optional, nor is it an afterthought with SecDevOps:
- All team members share equal responsibility for security
- Security policies are designed from the beginning (not necessarily implemented)
- Security considerations are given the highest weight for each stage in the SDLC and at deployment.
Note that one of the differences between SecDevOps vs DevSecOps is that when we consider information security as the number one priority in SDLC, the overall quality of our application code increases, and the development process speeds up. This is because the code is written securely from the beginning, and minimal modification is needed for security reasons in the later stages.
Contact us to get access to Nordic Defender’s Vulnerability Intelligence and level up your infrastructure’s cybersecurity.
Remember that a proper approach towards SecDevOps is educating all teams on different security aspects. Developers, QA testers, members of the operations team, and other employers should employ secure coding and secure development practices in their work.
There is also one more thing you should know before moving on. Never fall into the trap that says there is never too much security. Well, actually, there is too much security. So when should you feel alert about it? When security does not allow you to develop your application further and you seem to be stuck.
Different Types of SecDevOps
Still wondering which option suits you best between SecDevOps vs DevSecOps? Well, the first thing to do now is to learn more about different types of SecDevOps and see how each can benefit you.
Security as Code (SaC)
Security as Code (SaC) is one way to integrate SecDevOps into your workflow. It states that security must be combined into DevOps tools, security policies, and practices. In SaC, the development and security teams execute changes in the core infrastructure and test for bugs and vulnerabilities that are mostly mitigated with secure coding practices from the beginning.
Infrastructure as Code (IaC)
With the progress made in technology and innovations such as cloud computing and virtualisation, teams and organisations started using managed services for their infrastructure. Instead of deploying software on a physical server and dealing with system administrators, database administrators, QA testers, etc., you would just handle your IT infrastructure using configuration files. This enables you to take your mind off different security, optimisation, and productivity issues.
SecDevOps Best Practices
Just like DevSecOps, SecDevOps also comes with some best practices that increase the efficiency and effectiveness of software development. After we learn about them, it is high time we get to the main point of this article: SecDevOps vs DevSecOps.
Start Teaching Secure Development
Your first step towards SecDevOps should be training your developers to adopt secure coding practices. Keep in mind not to overtrain them to the extent they become security experts. Moreover, a red/black deployment strategy can help mitigate vulnerabilities in production environments. Maintaining two undifferentiated environments for production makes it possible to test new versions of code on production infrastructure without messing things up.
Pay Attention to People-Centric Security
A critical error some organisations make is that they fail to understand that it is people who make secure software applications, not tools. Security should be the number one responsibility of everybody on the team. Every employee must meet the security requirements in his role.
Establish Security Guidelines for Developers
One of the differences between DevSecOps vs SecDevOps is that a thorough SecDevOps pipeline designates security policies for different departments in an organisation. Secure coding practices, encryption rules, and software testing policies for using SAST, DAST, or SCA all contribute to the overall safety of the business.
SecDevOps vs DevSecOps
Finally, we are here to analyse the pros and cons of both methodologies and find the winner of the SecDevOps vs DevSecOps competition. Take a look at the following list to keep your mind in check:
- The agile framework mostly addresses the Design mindset (create a product or service that customers want now).
- DevOps and Continuous Testing framework mostly address QA mindset (verify a product or service works the way customers expect it to, when it is released, for all production configurations available at the time of the release).
- Site Reliability Engineering (SRE) framework mostly addresses the Operations (Ops) mindset (verify a product or service continues to work the way customers expect, for all production configurations, for the life of the product/service).
- DevSecOps, SecDevOps, and Continuous Security frameworks mostly address security mindset (defend valuables for the organisations that create/use a product or service against unintended and malicious actions by people and entities both inside and outside of the organisation).
DevSecOps Pros and Cons

Advantages of DevSecOps
Minimising the Cost of Vulnerability Detection
DevSecOps effectively reduces the number of detected vulnerabilities at later stages in the SDLC due to the automation of vulnerability discovery in the early stages. This means that less time and effort will be needed to fix vulnerabilities throughout the process, which in turn lowers the cost of vulnerability detection.
“Read More: How to Handle Zero-Day Vulnerabilities?”
Secure Code Production by Developers
Due to the fact that developers have a deeper knowledge of the application’s source code, they can estimate the impact of the vulnerabilities more accurately if they are trained in security. This is another reason why teaching security should be the first step in every organisation.
Rapid Response to Change and Requirements
If you are still not convinced to choose DevSecOps between DevSecOps vs SecDevOps, you should note that DevSecOps enables organisations to respond quickly to changes and requirements that come up. The flexibility of the structure in this methodology enables the implementation of any future technology changes.
Disadvantages of DevSecOps
Hard to Set Security as Top Priority
Most executives, especially C-level ones, have a rather broad, different point of view towards business. As a result, they might not put security as a top priority in their business, and they might not accept implementing the principles of DevSecOps.
Difficult to Find Vulnerabilities in Design
As we already know, both options in the comparison of SecDevOps vs DevSecOps are based on the Agile methodology. The most important principle in the Agile SDM is producing a Minimum Viable Product (MVP) as soon as possible so that the organisation can enhance the app based on user feedback later on. This, combined with the lack of proper documentation in the early stages, makes it tremendously difficult to find design-based vulnerabilities.
Lack of Proper Documentation at the Beginning
The lack of proper documentation in the early stages of SDLC makes software development a tedious, difficult task. The reason is that without the business logic in place, more resources will be lost until everything works out.
SecDevOps Pros and Cons
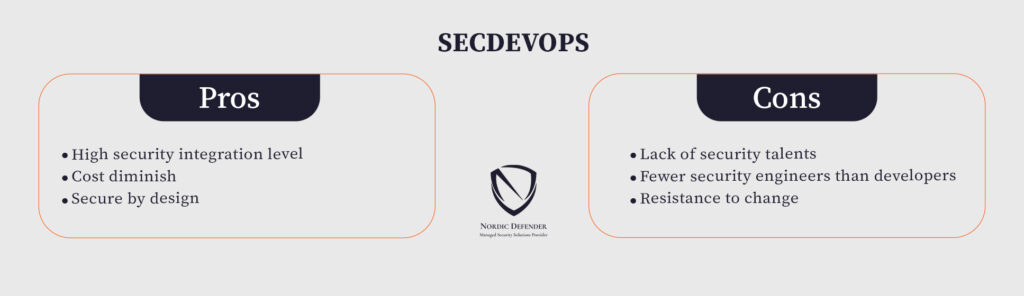
Advantages of SecDevOps
High Security Integration Level
If you choose SecDevOps in the battle of DevSecOps vs SecDevOps, you will see that security is integrated into every single stage of the SDLC. Not only is it integrated into every stage, it always comes first so that you can rest assured your application is being developed securely from the base.
Cost Diminish
We saw earlier that in the SecDevOps vs DevSecOps comparison, SecDevOps brings security closer to the beginning stages of software development. The faster you figure out the security and privacy errors, the less cost you impose on your business. Also, note that GDPR compliance penalties can go up to €10,000,000 or 4% of your whole business’s annual turnover. This is another reason you want to implement AppSec as soon as possible in your organisation.
Secure by Design
Integrating a secure-by-design approach into your business enables application developers in your organisation to be more productive and effective. This approach leads to the automation of security-based code reviews and AppSec testing.
Disadvantages of SecDevOps
Lack of Security Talents
If you are going to choose SecDevOps between DevSecOps vs SecDevOps, you should know that you might not be able to grow your security team to the extent you need. There is currently a shortage of security talent around the world.
Fewer Security Engineers than Developers
With fewer security experts than developers, your team is not going to be able to perform all the stages perfectly. A lack of human resources leads to a lack of time. You should not expect your security team to review all the changes made by the operations team or every piece of code your developers write.
Resistance to Change
Another disadvantage that SecDevOps has in the comparison of SecDevOps vs DevSecOps is that it requires a total paradigm shift. An immense change like this in culture will most probably be met with high resistance.
Which One Is the Winner?
There is no definitive answer to the question of who is the winner between DevSecOps vs SecDevOps. Every organisation needs to choose a methodology that best suits its product portfolio, business needs, the skills and experience of its development team, use case scenarios, and total business logic.
As a rule of thumb, though, you can most likely go with SecDevOps if you are developing an application from scratch and you are in your early stages; however, it may not be feasible to use it for codes that are decades old. DevSecOps is the better option for them.
Future of DevOps and Its Integrations
DevOps is a growing field, and there will be many more integrations of it coming in the future. That is why comparisons such as DevSecOps vs SecDevOps have a fixed part of DevOps in themselves.
Although what the future might bring may not be so clear to us right now, we should get ready for immense advancement in automation and monitoring technologies with the rise of machine learning and deep learning.
However, there is one thing that we can be sure of. Code standards, libraries and frameworks, and protocols will continue to change in the coming years as we see the shift from DevOps to either DevSecOps vs SecDevOps.
Final Word
In this SecDevOps vs DevSecOps article, we covered SDLC, its stages, and its different models, and we also talked about DevOps (DevOpsSec), DevSecOps, and SecDevOps. You can now make your decision knowing you know all there is to it.
Of course, you must keep in mind that today’s security field is very different from before. Everything changes so quickly due to the progressive nature of technology and science; for this reason, the future might bring some other things to light.
There is no right or wrong in the comparison of DevSecOps vs SecDevOps. It is only a matter of business decision. Both methodologies deliver high-quality end results if implemented correctly. So, do your research and implement what you think is best!
FAQ
What is the difference between DevSecOps and SecDevOps?
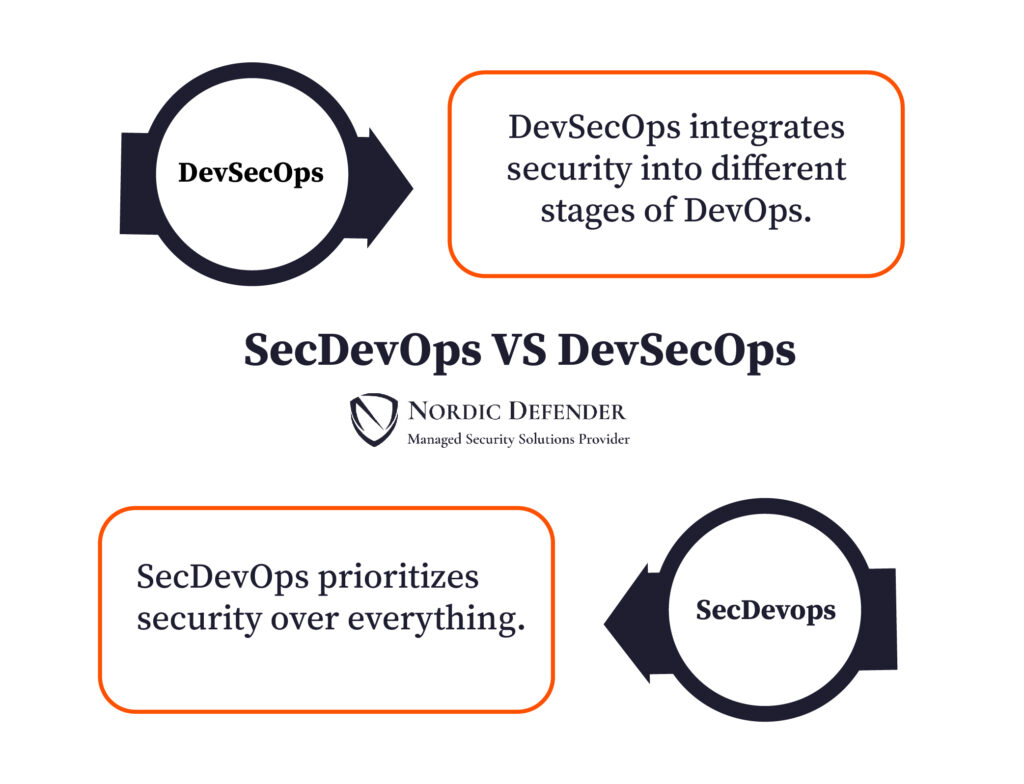
The main difference between DevSecOps vs SecDevOps is that DevSecOps integrates security into different stages of DevOps, whereas SecDevOps, quite unlike the pre-DevOps era, prioritizes security over anything.
What is SecDevOps?
SecDevOps is the most modern software development methodology in which the security of the applications is a priority, and all the stages of SDLC are based on secure coding practices.
Why is DevSecOps better than DevOps?
Well, DevSecOps is basically DevOps plus the Security component and is one way that security can be integrated into the DevOps process. Both DevSecOps and DevOps share the same mission; however, DevSecOps puts more emphasis on security.
Is agile part of DevSecOps?
No matter which you choose between DevSecOps vs SecDevOps, the choice you make comes from an Agile point of view. The Agile methodology is all about continuous, iterative development and testing between cross-functional departments.